Most breaches start with a stolen identity
AiTM Feed stops the attacks that steal them
Works with the security tools you already use
What Makes us Different?
Most threat intelligence is reactive - there has to be a victim before defences are shared. Microsoft's identification of Void Blizzard in 2025 was a fantastic insight into adversarial trade-craft, but multiple organisations had to suffer before those insights existed.
We do it differently. We hunt down adversarial infrastructure so you can block it before attacks start. The Void Blizzard infrastructure was in our feed weeks before Microsoft customers received their first phishing email. We were blocking ConsentFix campaign infrastructure before the technique had even been publicly disclosed.
That's the difference between proactive and reactive.
16k
Up to 16k new AiTM records per day
400%
We saw a 400% increase in AiTM activity between 2024 and 2025
23+
Additional feeds, allowing for further proactive blocking of malicious infrastructure
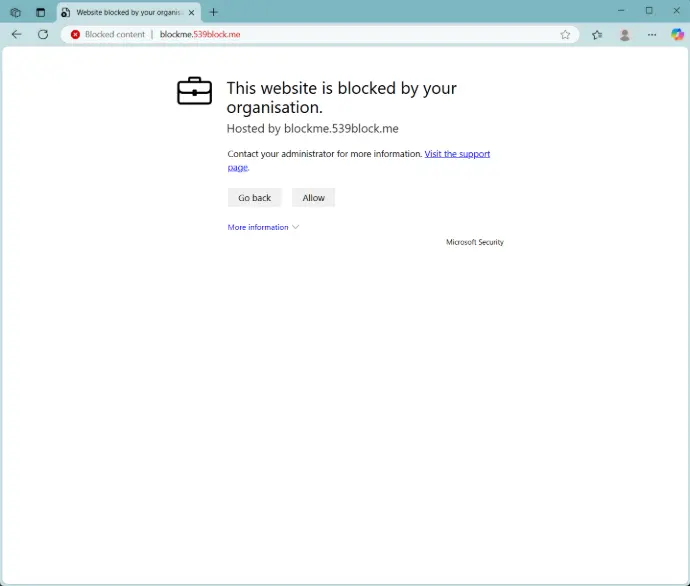
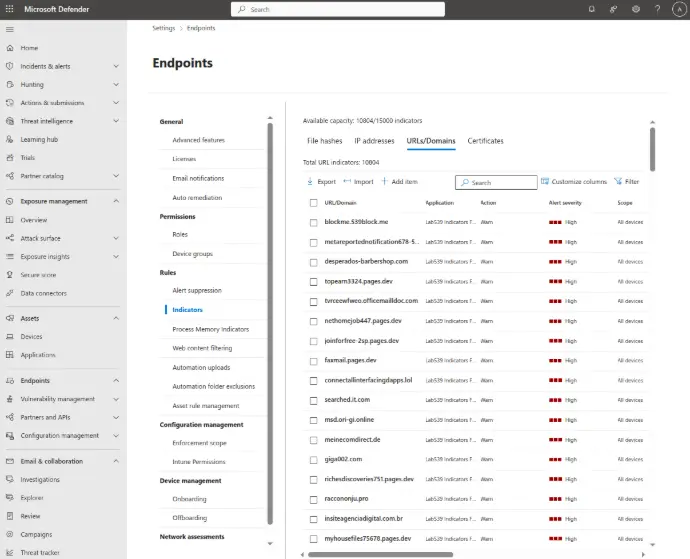
Seamless Microsoft Defender Integration
Simply enable this integration from within our portal and get indicators fed into your Microsoft Defender deployment in real time.
Block users from accessing AiTM infrastructure and raise alerts in your Defender dashboard when they do.
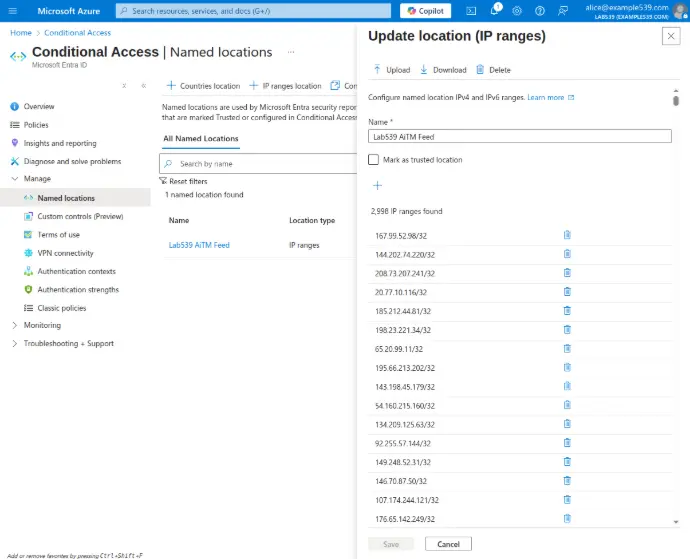
Conditional Access Policy Integration
Don't just prevent users from accessing AiTM infrastructure, but consume our named location feed in your conditional access policies in order to block authentication to your environment from AiTM infrastructure.
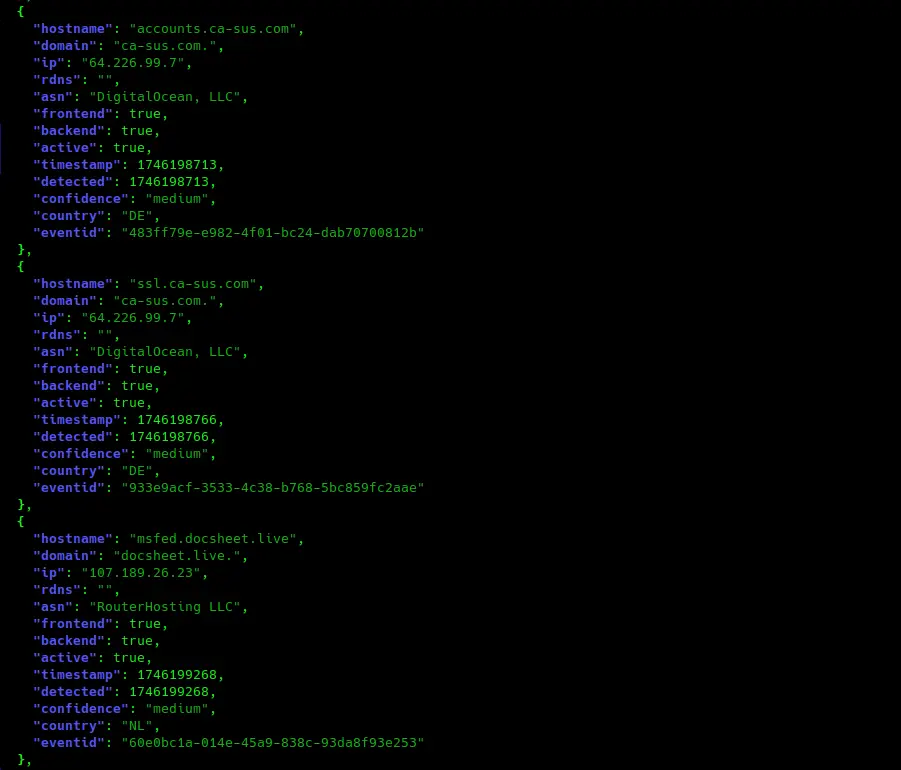
Full API access
We all have unique use cases, so we also make our data available in a flexible format via our API so that you can consume it however you wish.
We even let you pull down all recent data so you can run queries locally rather than via the API.
Great for custom use cases and great for investigations.
Our latest content
Check out our latest adversary tracking blogs:


